Introduction
Picture this: The UAE's oil flows smoothly through pipelines, refineries hum with activity, and gas platforms operate around the clock. But behind this seamless operation lies a digital backbone that's increasingly under threat. The UAE's oil & gas industry isn't just another business sector - it's the lifeblood of the nation's critical infrastructure, making cybersecurity not just important, but absolutely crucial.
As the UAE rolls out its National Cyber Security Strategy (NCSP), everyone's asking the same question: What will cybersecurity rules for oil & gas actually look like? The NCSP isn't just throwing around buzzwords - it's serious about sector-level governance and protecting Critical Information Infrastructure (CIIP). Each industry needs to tackle its own unique digital demons.
At EVOITSEC, we see first-hand that: oil & gas companies face significant cybersecurity challenges including operational downtime from DDoS attacks, aging SCADA systems with dangerous vulnerabilities, internal networks that might as well have revolving doors, under-resourced monitoring and untested IR runbooks, and supply chains that could be anyone's guess when it comes to security.
The NCSP Framework: Not Your Average Bureaucratic Exercise
This approach aligns with international regulatory trends, including the US NERC CIP standards for critical infrastructure and the EU's NIS2 Directive, while being tailored to regional needs. Instead of one-size-fits-all regulations, the NCSP recognizes that oil & gas has different needs than, say, banking or healthcare. Here's how it works: the national cyber authority sets the big-picture standards, while sector regulators work hand-in-hand with industry operators to make these standards actually work in the real world.
Think of it like this: the National Information Assurance Framework (NIAF) provides the blueprint, but it's up to the oil & gas regulator (working closely with the national cyber authority) to lead a sector-wide cybersecurity program. Companies won't just be checking boxes; they'll need to meet baseline controls, conduct meaningful risk assessments, and actively participate in protecting the nation's critical infrastructure.
The UAE's Information Assurance Standards (IAS) is a comprehensive set of controls built on international best practices like ISO/IEC 27001. But here's where it gets interesting: sector-specific guidelines will add another layer, specially designed for the unique challenges of industrial control systems in oil & gas operations.
The goal aligns perfectly with NCSP's "prepare and prevent" philosophy, raising the bar for cyber protection across every single entity in the sector, not just the big players.
The Real Problems Keeping Oil & Gas CISOs Awake at Night
When the Internet Decides to Attack: DDoS Nightmares
Oil & gas operations cannot afford any downtime. Whether it's online trading platforms executing million-dollar deals or remote field communications keeping operations running, a Distributed Denial-of-Service attack can bring everything to a grinding halt.
According to Siemens’ True Cost of Downtime 2024, the hourly cost of unplanned downtime in oil & gas can approach ~USD $500k during peak-price periods; 2023 showed a decline in O&G hourly downtime costs alongside oil prices, while 2022 recorded highs.
According to IBM's Cost of Data Breach Report 2024, the global average data breach cost reached $4.88 million, representing a 10% increase from the previous year, and much of that increase comes from operational downtime and lost customers. In an industry where minutes of downtime can cost hundreds of thousands of dollars, DDoS protection isn’t a luxury - it’s an operational-continuity insurance. This is why EVOITSEC in particular puts so much emphasis on the prevention of DDoS.
Incident Response: The "We'll Figure It Out When It Happens" Approach
Some companies operate under the dangerous assumption that cyber incidents won't happen to them. Others know they will happen but haven't prepared for when they do. The result? Security monitoring that's more reactive than proactive, and incident response plans that exist more on paper than in practice.
One real-world example: A company had virtually no incident handling procedures and poor monitoring systems. During a simulated insider threat test, sensitive data was exfiltrated through a backup system that no one was watching. The wake-up call led to new detection rules and a complete overhaul of their incident response plan.
Supply Chain: The Weakest Link You Didn't Know You Had
The oil & gas industry operates on a complex web of suppliers, contractors, and partners. Each connection is a potential entry point for attackers. A red-team exercise for a logistics company in the oil & gas supply chain revealed critical vulnerabilities that prompted the client to implement a complete Zero Trust policy.
The reality is that your cybersecurity is only as strong as your weakest supplier, and many companies are just beginning to understand what that really means.
What Future Oil & Gas Cybersecurity Rules Might Look Like
Based on the NCSP framework and the real-world challenges facing the industry, here's what we can expect.
Baseline Security: No More "We'll Get to It Later"
Every oil & gas operator will likely need to implement an information security management system (ISMS) that meets UAE IAS/ISO 27001 standards. This isn't about paperwork. It's about creating a culture where cybersecurity is baked into daily operations. Regular compliance audits won't be suggestions; they'll be requirements.
Industrial Control Security: Treating OT Like It Matters
Given how critical operational technology systems are, sector rules will almost certainly include specific requirements for ICS/SCADA environments. We're talking about real network segmentation between IT and OT, strict access controls for control networks, mandatory firmware updates, and adherence to standards like IEC 62443.
Companies will probably need to conduct annual ICS security audits or resilience tests to actually find and fix vulnerabilities before attackers do.
Risk Assessment: Making It Real and Regular
The regulator will likely require periodic risk assessments at both company and sector levels. For major operators, this could mean annual penetration testing or red-team exercises, with results (or at least summary reports) submitted to the regulator.
This isn't busy work - it's about identifying common threats across the sector and addressing them collectively, exactly as the NCSP envisions. Risk assessments are like health checkups: missing it is grossly irresponsible.
24/7 Monitoring: Someone's Always Watching
Future rules will probably mandate minimum logging and monitoring capabilities - think intrusion detection systems, SIEM solutions, and either an in-house 24/7 SOC or a contract with a professional managed SOC service.
Companies will also likely need to report significant cyber incidents to a national CERT within a specific timeframe and maintain up-to-date incident response and recovery plans that actually work when tested.
According to Mandiant M-Trends 2025, the global median dwell time was 26 days when incidents were discovered by external entities, versus ~10 days when discovered internally - a strong case for in-house monitoring and SIEM/EDR
Supply Chain Security: Trust, But Verify (Everything)
Building on CIIP principles, oil & gas cybersecurity regulations will probably extend to critical suppliers. This means due diligence requirements, cybersecurity clauses in contracts, ensuring vendors follow security best practices, and participating in industry information-sharing programs.
The NCSP emphasizes cooperation between critical sector entities, so we might see the emergence of an oil & gas sector Information Sharing and Analysis Center (ISAC) to facilitate threat intelligence sharing and best practice development.
NCSP → Likely O&G Controls (examples)
- Prepare & Prevent → Baseline Security: ISO/IEC 27001/IAS ISMS; asset inventories (IT/OT); patch baselines and hardening; backup/restore drills (RTO/RPO).
- OT/ICS Protection: IT/OT network segmentation; jump-hosts with MFA/ZTNA; allow-list on HMIs/servers; IEC 62443-aligned change control; firmware currency; vendor remote-access isolation.
- DDoS & Availability: always-on L3/L4 (Stormwall) + L7 application protection (WAF/bot management); tabletop drills; runbooks with clear roles.
- Identity & Access: MFA for all privileged and vendor accounts; PAM/credential hygiene; device posture checks before access (ZTNA/NAC).
- Data & Email: data classification + DLP; DMARC/SPF/DKIM; secure email gateways; anti-BEC rules.
- Cloud/SaaS: CSPM/CNP baselines; sanctioned-apps registry (CASB/SASE); secrets & key hygiene in CI/CD (DevSecOps).
- Monitoring & Response: centralized logging; SIEM use-cases; 24/7 SOC (in-house or managed); MTTA/MTTR targets; mandatory incident reporting to national CERT.
- Supply Chain: TPRM questionnaire; security annex in contracts; attestation cadence; evidence sampling; revocation process for non-compliant vendors.
A 90-Day NCSP-Aligned Action Plan
Days 0–30 (Stabilize)
- External “X-Ray” (48h): external asset map, misconfig & exposure list; quick wins.
- Always-on DDoS: L3/L4 (Stormwall) + L7 (WAF/bot) for internet-facing systems.
- MFA for all admin/vendor accounts; disable direct admin RDP; use jump-hosts.
- SIEM onboarding of crown-jewel systems; 10 critical use-cases live.
Days 31–60 (Harden)
- IT/OT segmentation changes in maintenance windows; restrict east-west.
- EDR rollout to servers/workstations; policy tuning; USB/media policy.
- Email posture: Secure Email Gateway (SEG), DMARC=reject, BEC rules; awareness sprint #1.
- Cloud/SaaS CSPM baseline; secrets hygiene in CI/CD; quality gates in pipeline.
Days 61–90 (Prove & Govern)
- Tabletop drill (DDoS + insider); measure MTTA/MTTR; IR runbooks v1.
- Red-team/targeted pentest on remote access + OT jump path.
- Vendor tiering + security annex rollout; evidence sampling of critical suppliers.
- ISMS improvements log; management review; KPI dashboard to executives.
The Business Case: Why This Investment Makes Sense
Let's talk numbers. According to IBM's 2024 report, the Middle East sees an average data breach cost of $8.75 million - the second highest globally. For oil & gas companies, where operational downtime can cost exponentially more, investing in cybersecurity isn't just compliance; it's financial survival.
Here's an encouraging number: IBM research shows that organizations extensively using AI and automation in their security operations experienced $2.2 million lower breach costs than organizations with minimal or no AI. The lesson? Proactive measures - like those likely to be mandated - can dramatically reduce both incident costs and risk exposure.
The following hypothetical scenario, based on real-world attack patterns observed in the oil & gas sector, illustrates the importance of proactive detection systems:
Threat: a cyber attack on the critical infrastructure aiming to disrupt the production. The attackers used sophisticated targeted malware disguised as legitimate software.
Let’s compare:
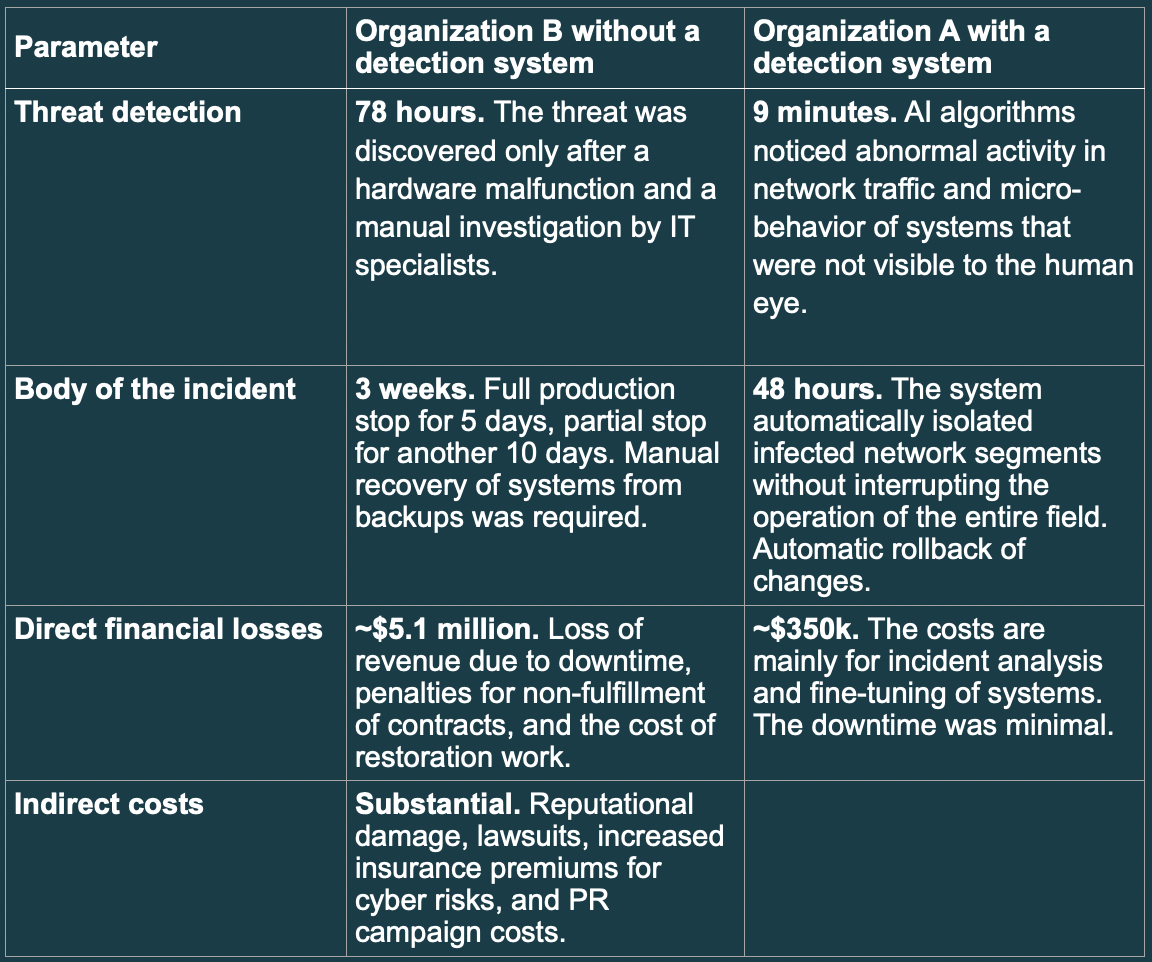
It is clear to see in the table above that the costs of implementation of a prevention policy and detection system are outmatched by possible harm of downtime and financial cost of an incident.
How We’ll Measure It (KPIs)
- Availability: unplanned downtime (min); DDoS time-to-mitigate; drills passed.
- Exposure: # external criticals; % systems behind WAF/anti-bot; DMARC=reject.
- Identity: % MFA coverage by role/vendor; # privileged sessions via jump-hosts.
- Detection/Response: MTTA/MTTR; % incidents auto-contained by EDR/SIEM.
- OT Safety: # unauthorized changes in control networks; firmware currency %.
- Supply Chain: % critical suppliers with attestation; # with corrective actions.
- Training: phishing failure rate by role; re-test improvement %.
- Risk: estimated loss avoided (downtime per hour × avoided hours).
EVOITSEC & Stormwall's Solution: Getting Ahead of the Curve
For oil & gas companies that want to stay ahead of upcoming regulations, EVOITSEC and Stormwall have developed something called the Preventive Pentest & Protection (P&P) bundle. It's designed to address many of the challenges we've discussed, combining deep penetration testing expertise with proven DDoS protection and managed security services.
The Quick Health Check: 48-Hour Security X-Ray
The process starts with what EVOITSEC calls an "external X-ray" - a rapid assessment of the company's security posture delivered in just 48 hours. This pre-audit mapping identifies external assets and weaknesses, cutting down the discovery phase of a full audit by about 30%. It's like getting a security MRI before the full physical exam.
Red Teaming: The Real-World Attack Simulation
Next comes a full-scale red team exercise that simulates actual attack scenarios. EVOITSEC's certified team conducts covert reconnaissance, attempts phishing and social engineering for initial access, then tries to move laterally through the network to reach critical systems.
These aren't theoretical exercises. Real red team simulations have uncovered issues like misconfigured remote access to SCADA systems and internal segregation that existed more on network diagrams than in reality. The detailed reporting and debriefing that follow provide a clear roadmap for fixing identified vulnerabilities.
DDoS Protection: The Always-On Shield
Here's where the P&P bundle goes beyond just finding problems - it immediately helps solve them. Stormwall deploys always-on DDoS filtering to protect the company's online infrastructure. Their distributed network of scrubbing centers can mitigate attacks closer to their source, preventing the downtime and financial losses that can devastate oil & gas operations.
The solution covers all attack vectors - network floods, application-layer attacks, you name it - filtering malicious traffic across layers 3-7 of the OSI stack. For an industry where any operational outage can be catastrophic, this proactive filtering is a game-changer.
What’s in the P&P Bundle
- 48-Hour “External X-Ray”: external asset map, misconfig & exposure list; quick wins (~30% discovery time saved).
- Red Team (O&G-aware): social/remote access, lateral movement to crown jewels; OT jump-path checks.
- Anti-DDoS: Stormwall L3/L4 always-on + L7 via WAF/bot management; drills and runbooks.
- Managed Detection: SIEM use-cases + EDR auto-containment; optional 24/7 monitoring.
- Risk & Governance: incident reporting templates, supplier security annexes, KPI dashboard for executives.
Local Security Center in the UAE for Traffic Filtering
The P&P bundle also includes local Security Center services in the UAE. This enables effective filtering of malicious traffic and stable operation of frontend systems.
Integrated Risk Management: Making It All Make Sense
EVOITSEC ensures that all findings and protective measures tie back to overall risk management. By combining internal technical audits with external risk assessments, clients get 360-degree risk coverage with no blind spots.
Executives receive clear visibility into how each vulnerability or incident could impact business objectives, bridging the gap between technical details and enterprise risk management.
The ROI Story: When Security Pays for Itself
The return on investment for the P&P approach is well-documented. Benefits like blocked phishing attempts and avoided breach fines mean the bundle typically pays for itself in under 12 months. In one engagement, a successful phishing exploit was prevented during the red team phase, averting a potential breach that could have cost far more than the entire security program.
As one Deputy Managing Director of a Middle Eastern oil & gas company put it: "EVOITSEC-FZCO is one of the most skilled and professional teams in the field of information protection and cybersecurity... a very reliable and competent service provider for oil & gas and basic infrastructure enterprises."
The Bottom Line
As the UAE moves toward formalizing sector-level cybersecurity rules for oil & gas, companies should expect a strong focus on governance, resilience, and proactive defense. The regulations won't just be about compliance, they'll be about creating a more secure, more resilient industry.
Smart companies are already getting ahead of the curve. By implementing comprehensive solutions like the EVOITSEC Preventive Pentest & Protection (P&P) Bundle and aligning with international standards now, oil & gas enterprises can not only stay ahead of regulations but also significantly reduce their cyber risk.
Our end goal? An industry that keeps the oil flowing and the lights on while contributing to the UAE's broader national cyber resilience objectives.
Do our goals match?
